weekly
Written by: Kong Xiangwei
2020-10-30 17:50
Last update date: 2020-10-30 17:50
In mid-September, a 78-year-old severely ill woman in Germany was sent to Düsseldorf University Hospital for treatment. However, 30 servers in the hospital were hacked with ransomware and could not receive emergency patients. She was forced to be transferred to a hospital in Wuppertal, 30 kilometers away, where she was delayed for an hour before receiving treatment and eventually died.
Related vulnerabilities allow hackers to use ransomware to encrypt and seize data, forcing the victim to pay a ransom.
German prosecutors are investigating the connection between the patient’s death and hackers. Ciaran Martin, the former chief executive of the UK’s National Cyber Security Centre, said: “If it is true, this tragedy will be the first case in the world that I know of related to a cyber attack that caused human death ."
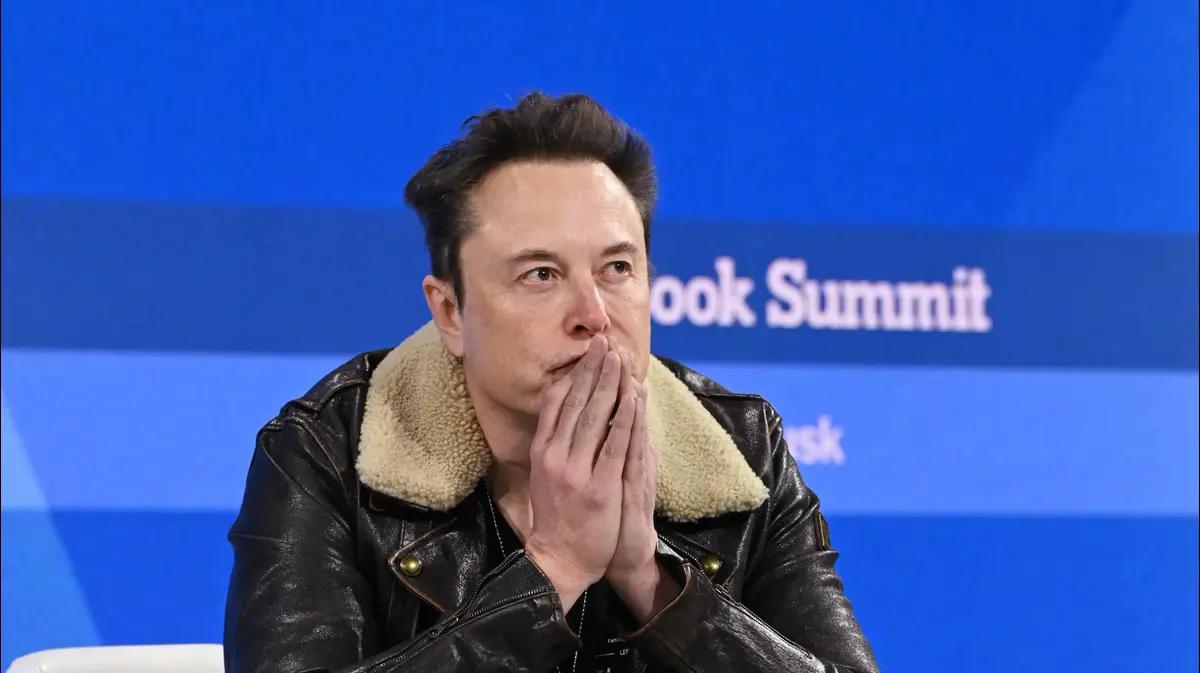
Recently, a patient in Germany is suspected to have died due to a hacker attack on a hospital.
Many medical institutions around the world have suffered hacker ransomware attacks under the new crown pneumonia epidemic.
(Getty Images)
Hackers take advantage of the chaos to blackmail
During the epidemic, many medical institutions were also targeted by hackers.
The Czech Republic’s largest new crown pneumonia testing center and the Brno University Hospital in Brno (Brno), the second largest city in the Czech Republic, suffered a ransomware attack and was forced to disconnect from the Internet in March, delaying the test results and some operations, and some patients were even more affected. Transfer.
The American medical software company eResearchTechnology was also blackmailed by hackers in September.
The hacking forced the experimenters to switch to paper and pen records. The affected customers include the research institute Quintiles (IQVIA) and the pharmaceutical company Bristol Myers Squibb (Bristol Myers Squibb), the former assisting the pharmaceutical company AstraZeneca in managing the new crown vaccine Research and development, the latter is leading a research and development alliance for rapid testing of new coronary pneumonia.
On the other hand, the epidemic "created" opportunities for various cyber attacks.
As early as the beginning of the epidemic, hackers grasped the panic and anxiety of the people everywhere and launched phishing attacks with virus information as bait; hackers pretended to be government employees who tracked contacts and sent phishing spam messages; there were also hackers who stolen. Taking personal data to falsely claim unemployment benefits...
Many information security professionals have observed that various cyber attacks have increased during the epidemic.
(Getty Images)
According to observations by some security companies, ransomware attacks doubled during the epidemic.
Israeli information security industry Check Point pointed out in early October that the average daily ransomware attacks in the third quarter of this year increased by 50% compared with the first half of this year.
The ransom negotiating company Coveware reported that as of the second quarter of June this year, the average ransom payment for all industries increased by 60% to nearly $180,000.
Overall, cyber attacks are also increasing.
According to Eugene Kaspersky, the founder of antivirus software vendor Kaspersky, told the British Daily Telegraph in September: "In June and July, (cyber attack) activity increased by 20% to 25%. In the new crown pneumonia Before the outbreak, our capture volume was more than 300,000 new malicious files per day, and now the virus laboratory reports that more than 400,000 new malicious programs are captured every day."
Outside of medical institutions, cyber attacks also cause companies to suffer heavy losses.
For example, the Israeli financial technology company Sapiens paid a ransom worth $250,000 in Bitcoin after being threatened by hackers to shut down the company's network.
Under the epidemic, remote work and study have become the new normal, which also provides hackers with more attack opportunities.
(Getty Images)
Security breaches increased
The global implementation of social distancing measures has brought a new normal in life, and a new cyber security crisis has also followed.
When all walks of life follow the "transformation" of technology companies such as Facebook and Twitter and work remotely, as Kaspersky pointed out: "Very few companies can provide the same security measures for working at home as they do inside the company." University of Melbourne Computer and Information Suelette Dreyfus, senior system lecturer, added that, on the one hand, home Wi-Fi systems "may have not been updated in the past five years, so there are naturally security risks." Security risks.
Also sufferers are schools that implement distance learning.
The Clark County campus in Nevada, USA, with about 320,000 students, was hacked into the server for extortion after three days of online teaching at the end of August, and some files could not be opened.
The school refused to pay the ransom. As a result, hackers disclosed the social insurance numbers, addresses and retirement documents of the faculty and staff, as well as personal information such as the student's name, grade, date of birth, address, and school.
Some school districts that have been hacked think that it is more expensive to rebuild the server, and may delay the teaching schedule for several weeks, so they choose to pay the ransom.
During the epidemic, many medical institutions have added UV disinfection robots, but this is not safe because the robots can be taken over remotely.
(Getty Images)
In addition, the epidemic has caused many industries to become "Amazonization" and accelerate the transformation of automation and mechanization, but these robots are not necessarily safe.
Federico Maggi, a researcher at the digital security company Trend Micro, and Marcello Pogliani, an information security researcher at the Politecnico di Milano, Italy, published a research report in early August. They found defects in the software produced and distributed by ABB, a major industrial automation system manufacturer in Sweden and Switzerland; they are still very popular in the industry. Vulnerabilities have been found in the open source software Ros-I, which is welcome and suitable for ABB and German robot manufacturer Kuka.
ABB has fixed related vulnerabilities.
Many medical institutions have added UV disinfection robots, but Oscar Lage, head of cybersecurity and blockchain at Spanish research and innovation company Tecnalia, reminded: "Most robots are systems with poor security. Design, create and sell. Their people only care about their functions."
(Excerpt)
The above is excerpted from the 237th issue of "Hong Kong 01" Weekly (October 27, 2020), "Ransomware Attacks Multiply Network Security Facing New Threats" If you want to read the full text, please
click here to
sample the weekly newsletter and browse more in-depth reports.
Selected content of 237 issue of "Hong Kong 01" Weekly News:
[Cover report] Cathay Pacific learned that Hong Kong’s epitome is time to reorganize its aviation industry planning
What is wrong with Hong Kong's governance?
The government plans to set up factories in Hong Kong
Presidential election final debate: Trump missed the opportunity, Biden won
Battery technology advances into the "electric age"
London Experience Urban Agriculture: Enclosure planting becomes a trend
Witness the animal carcasses spreading across the wild, like purgatory cruelty to animals. Rescue is valuable!
01 Weekly report in-depth report on cybersecurity of computer hackers with new crown pneumonia





/cloudfront-eu-central-1.images.arcpublishing.com/prisa/WQEEUVRP3BB57M7LND37U7VREE.png)








